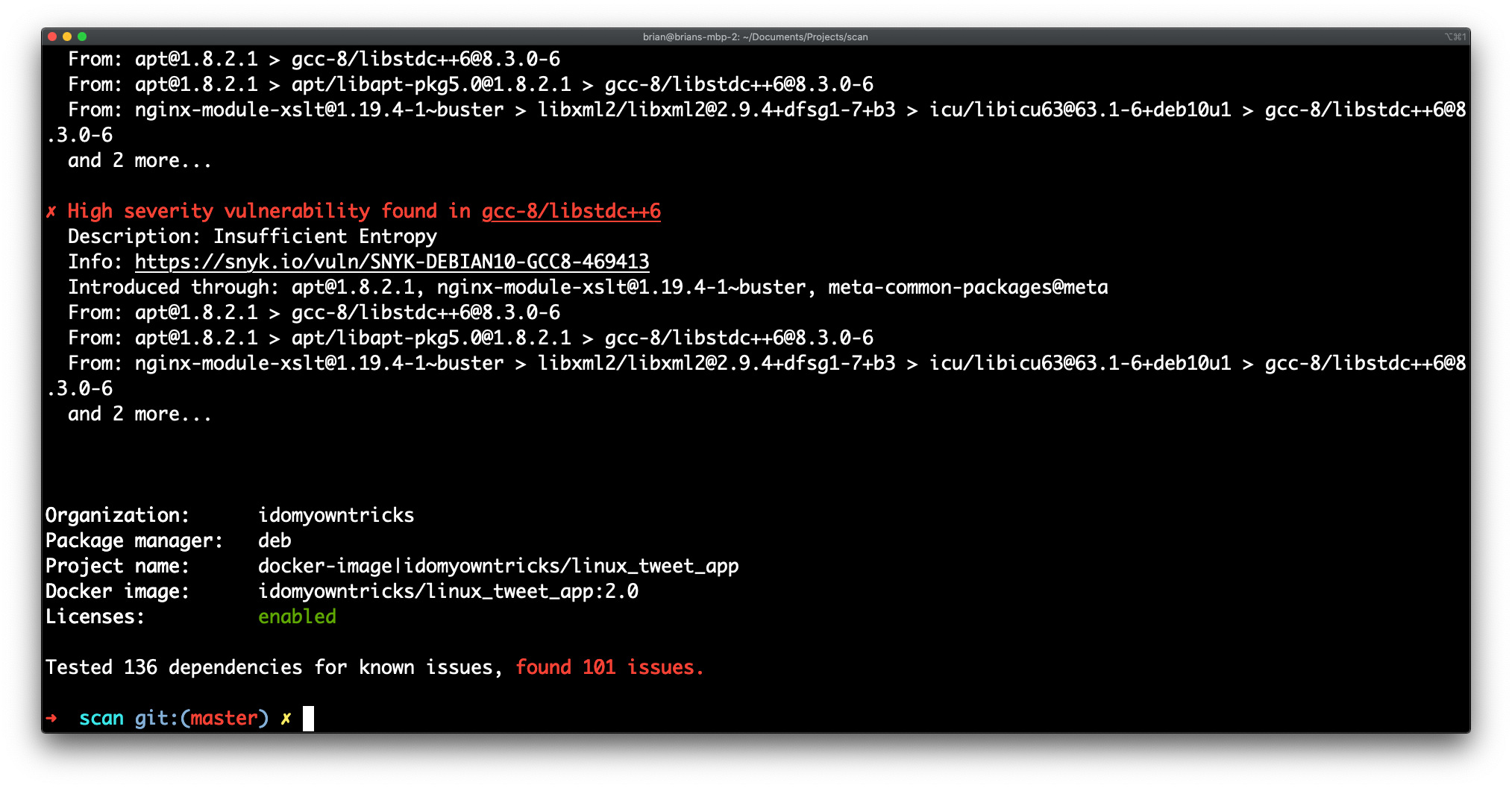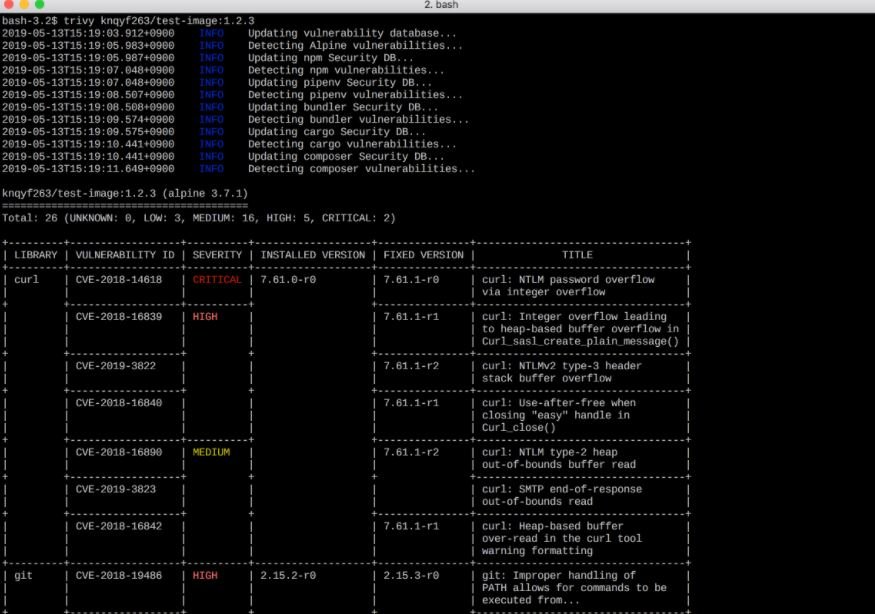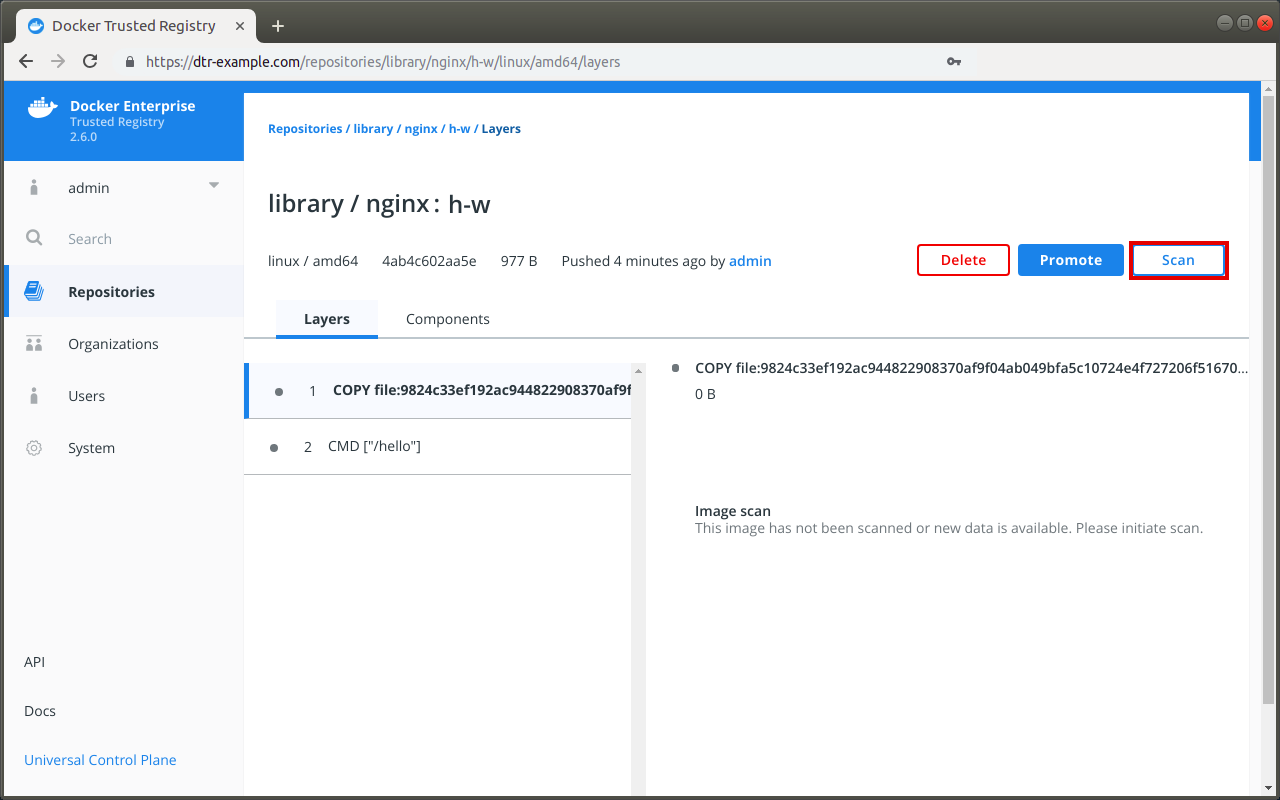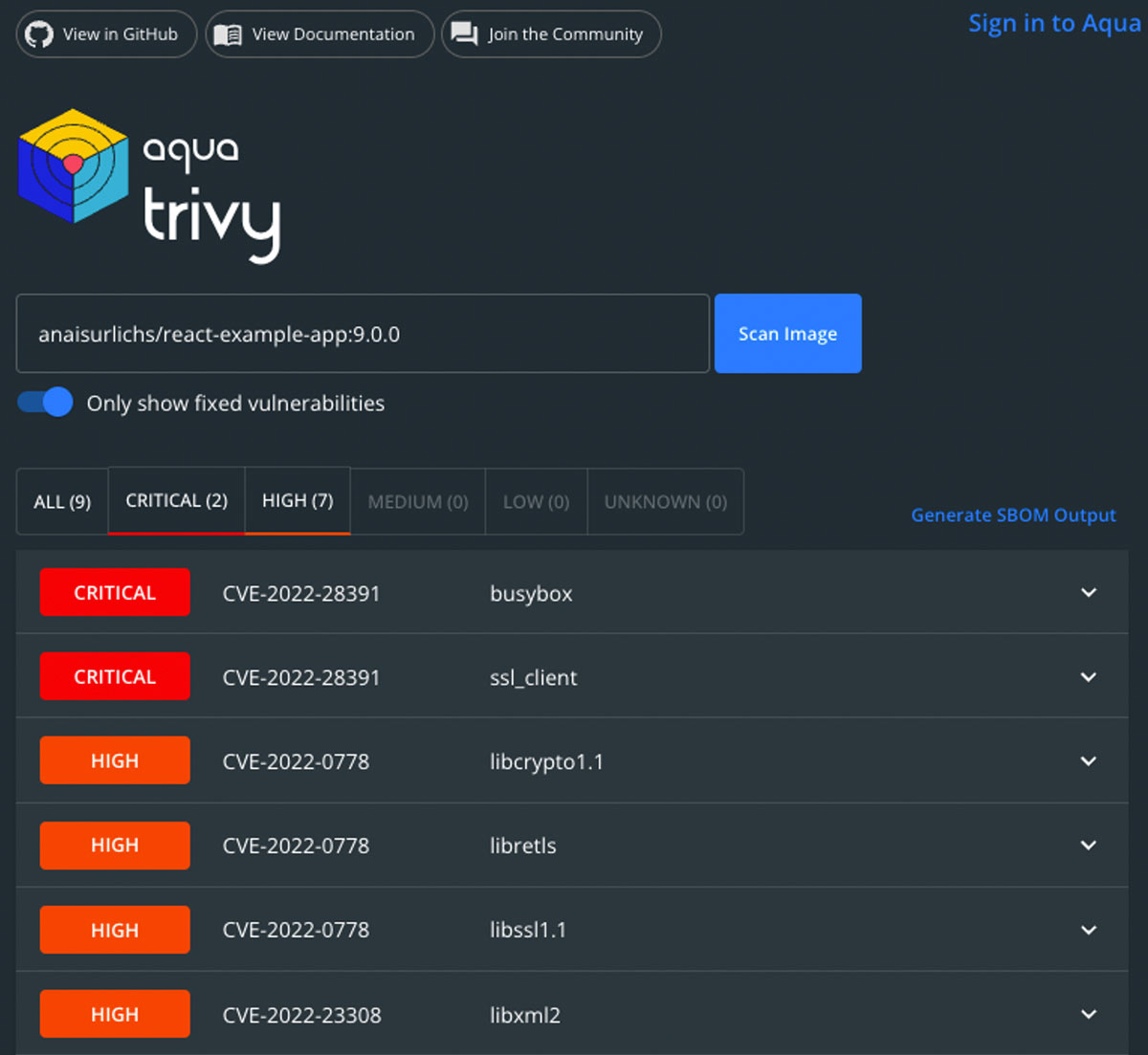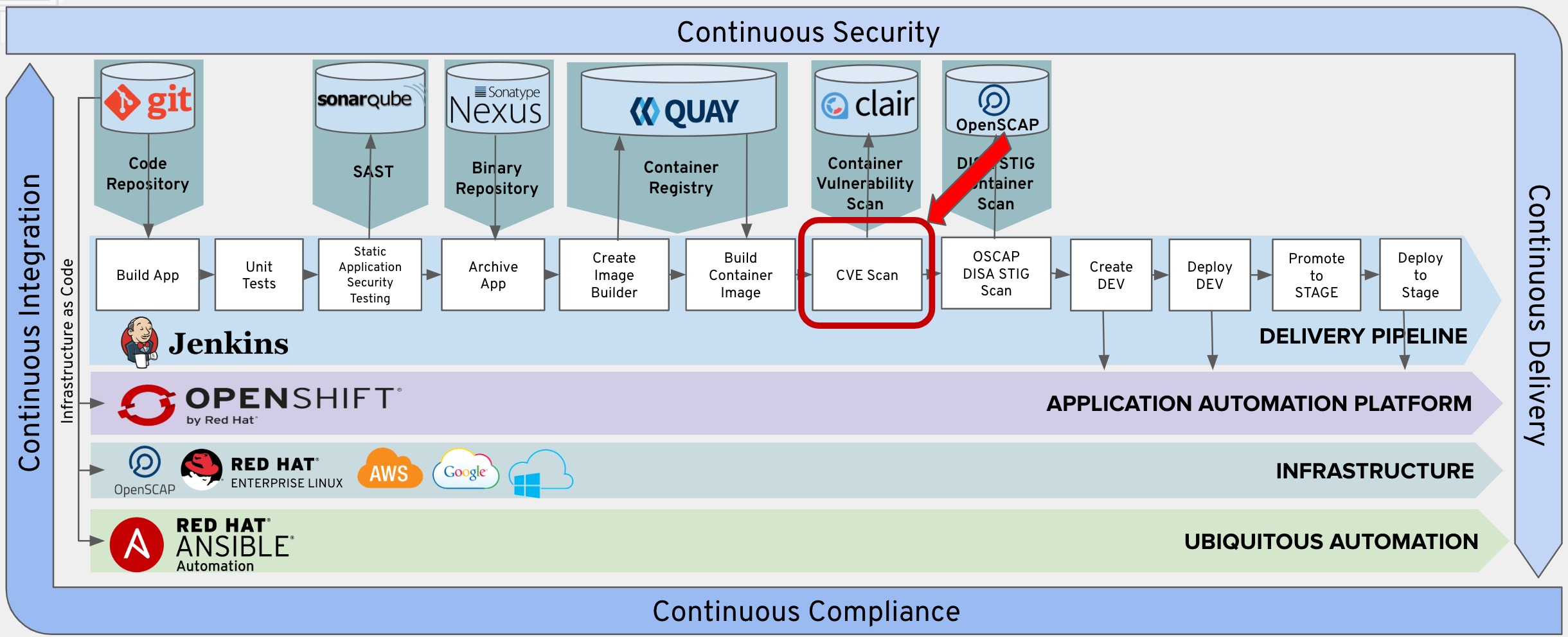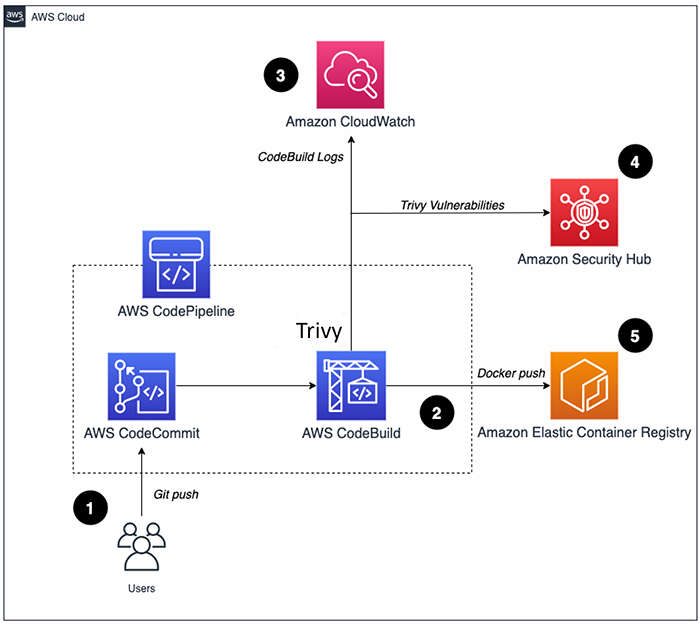
How to build a CI/CD pipeline for container vulnerability scanning with Trivy and AWS Security Hub | AWS Security Blog

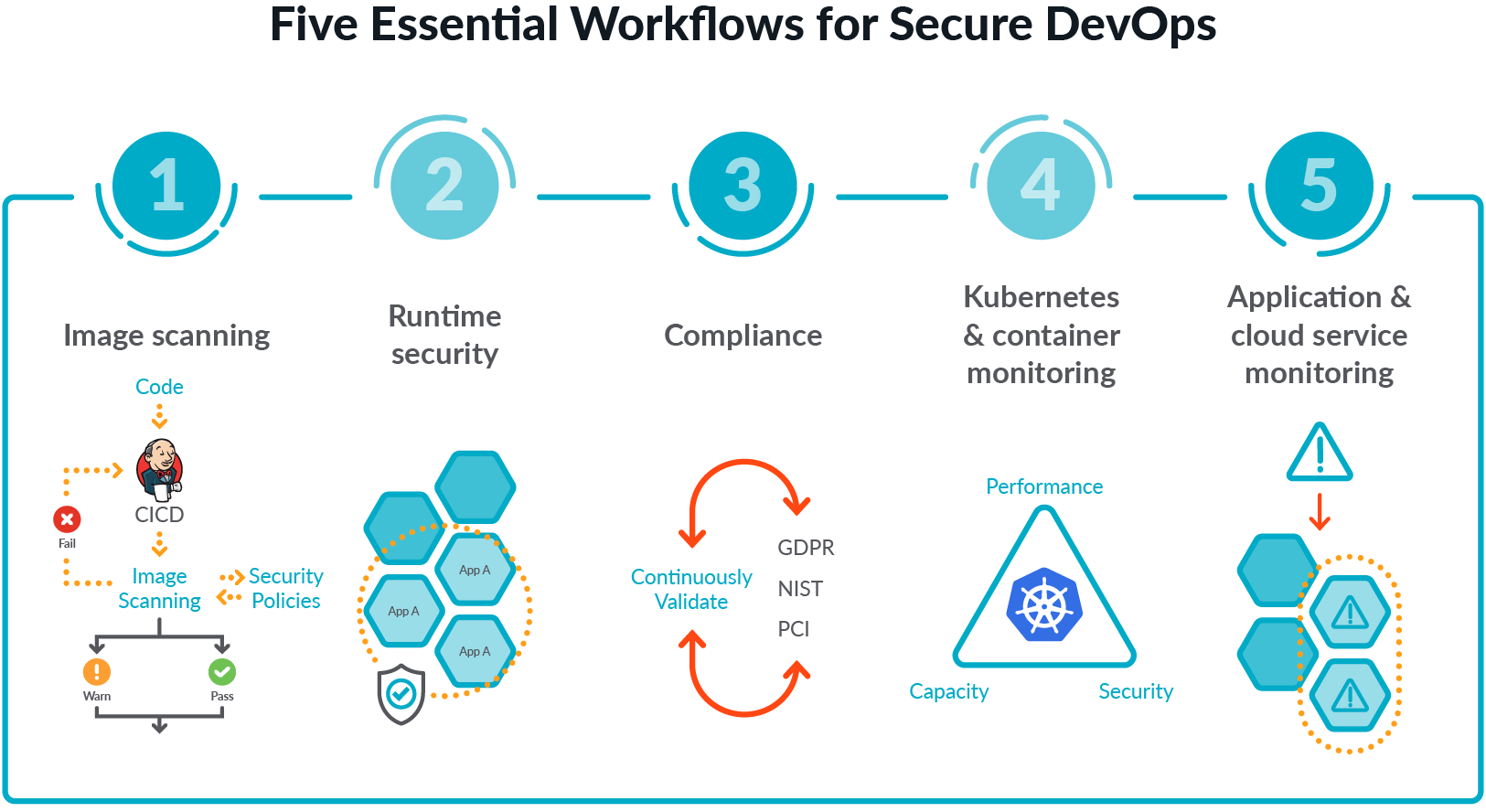
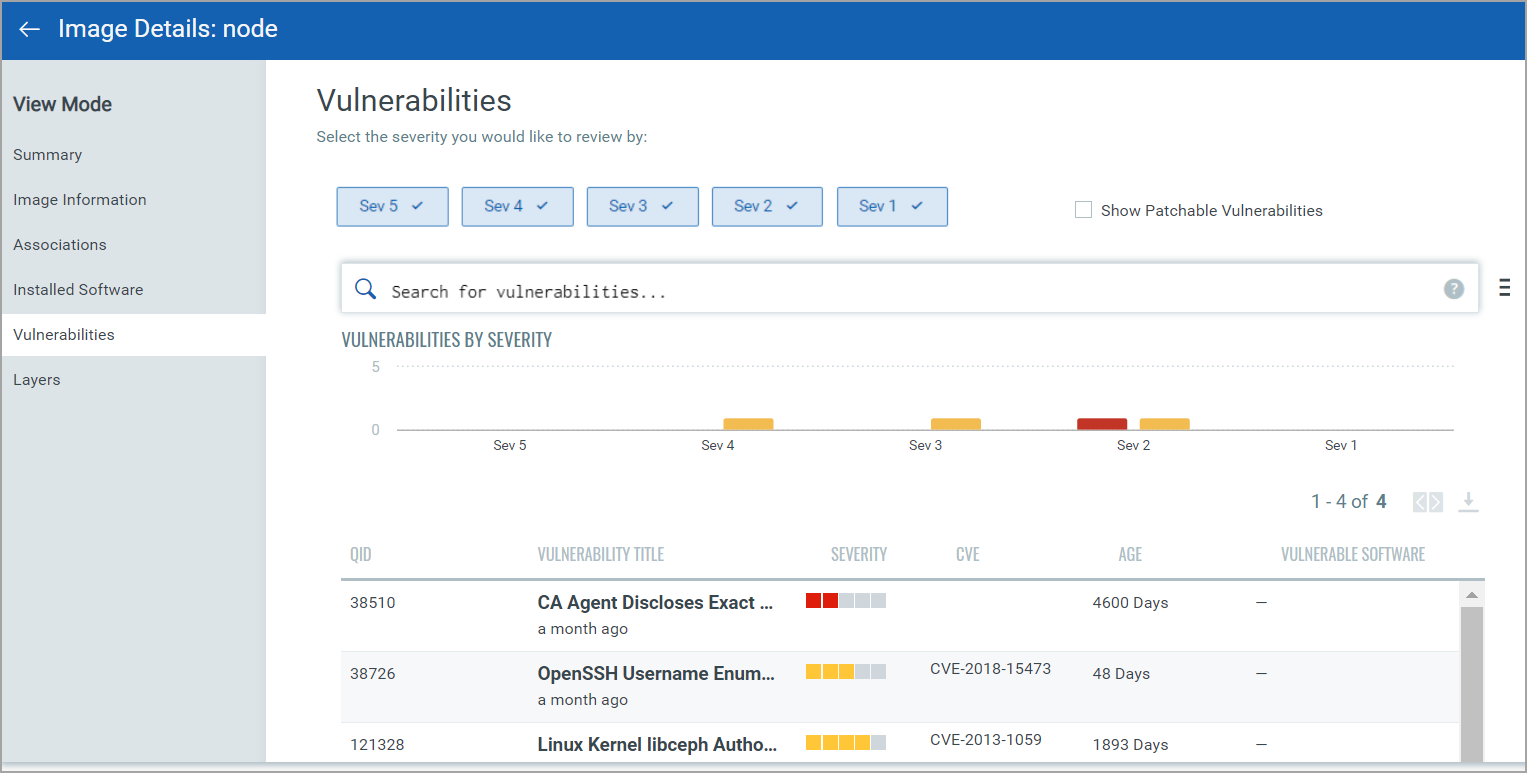
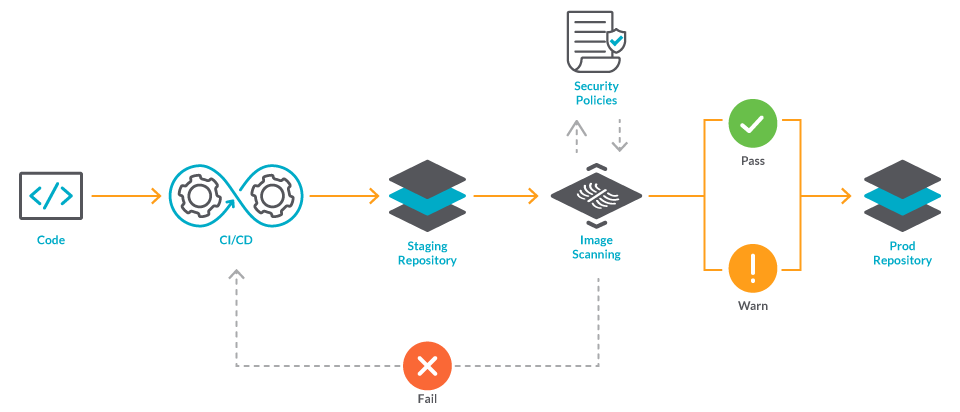
JFrog and Docker Unveil Integrated Solution for Increasing Container Security & Developer Productivity

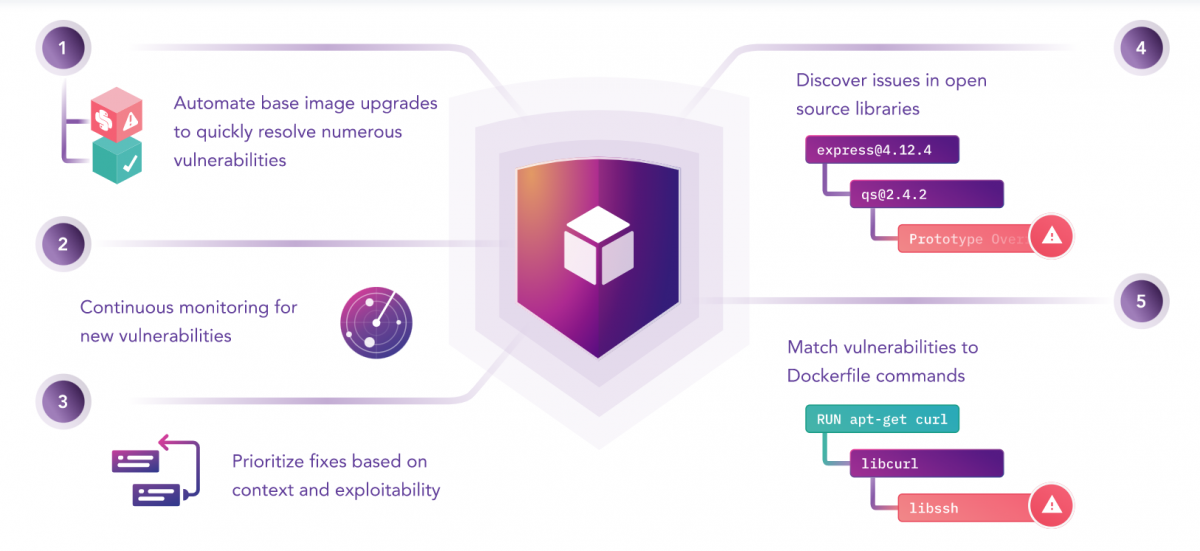
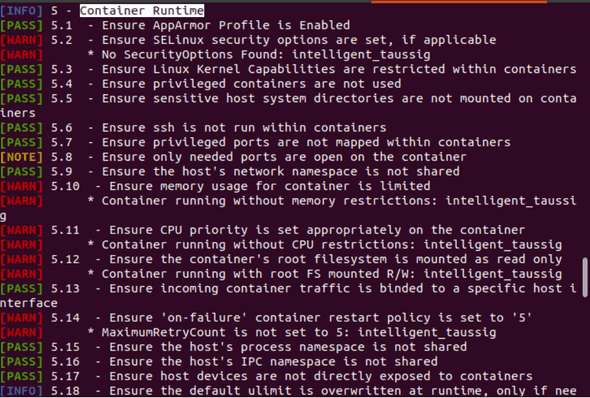
Introducing Container Image Scanning: Identify both misconfigurations and vulnerabilities with Bridgecrew