How to use NMAP – which is the “right” NMAP scan to use? | University of South Wales: Cyber University of the year: Three years running: 2019, 2020, 2021

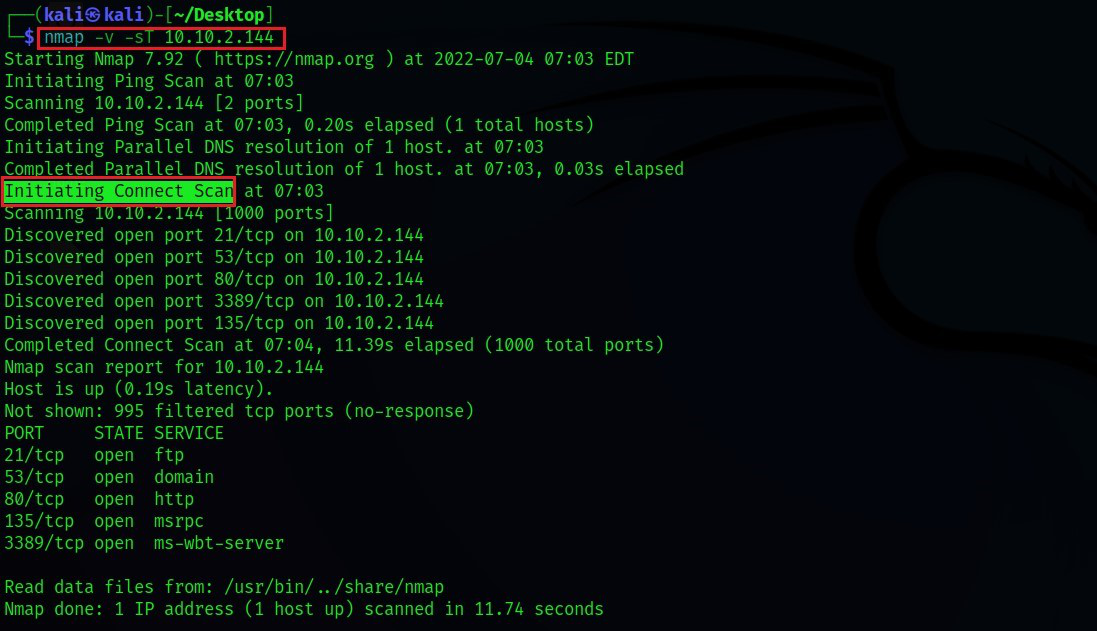
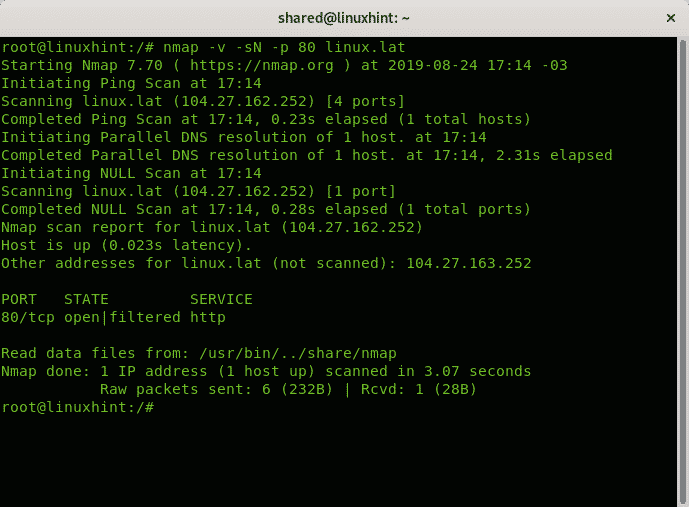
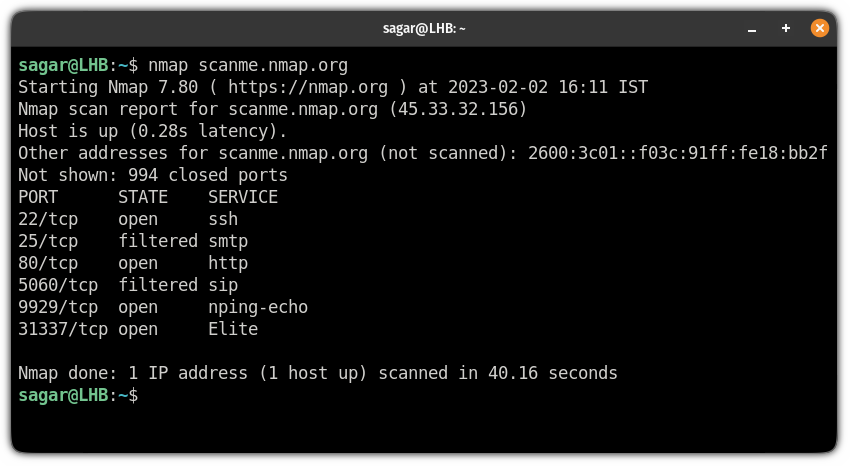
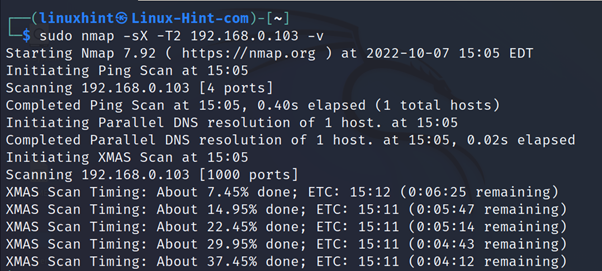
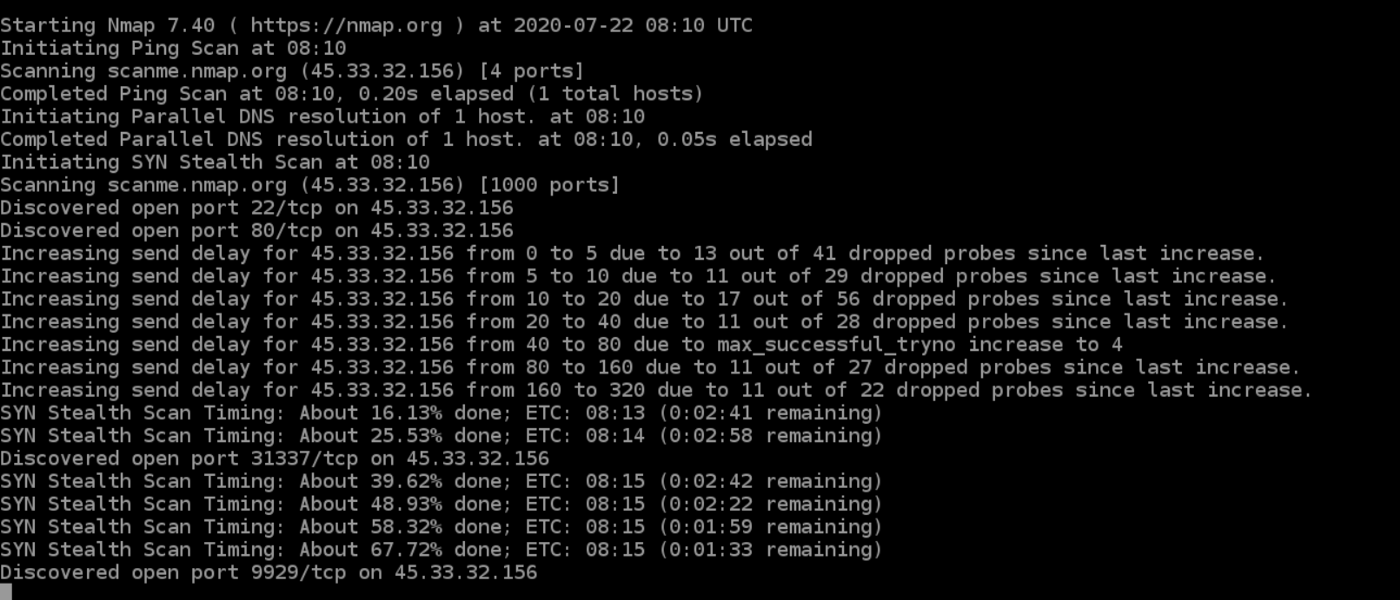
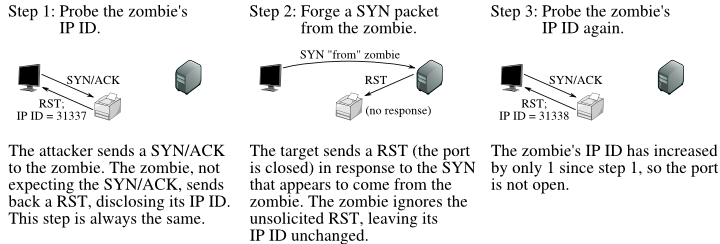
Nmap cheat sheet: From discovery to exploits, part 2: Advance port scanning with Nmap and custom idle scan | Infosec Resources